ECM retention policy in 2026 for stronger records management, legal hold, compliance, and policy-driven document lifecycle control.
Problem-driven introduction
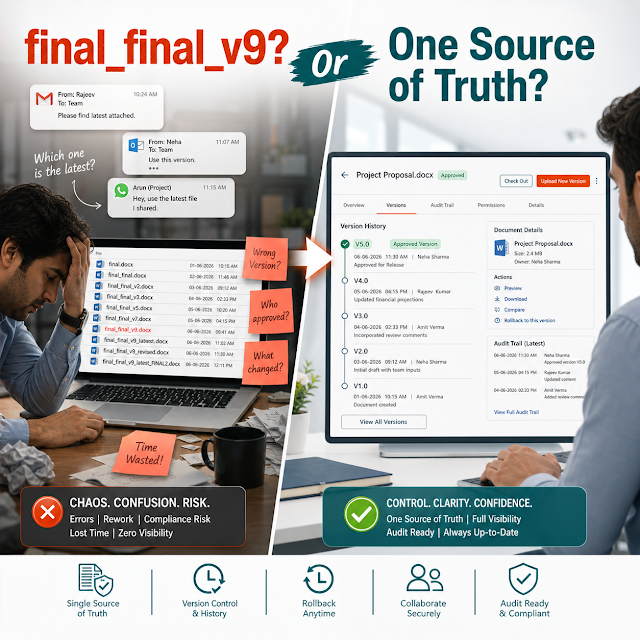
Most organizations don’t “fail compliance” because they lack documents. They fail because they can’t prove the right version was retained for the right period, protected against tampering, discoverable in time, and disposed of defensibly when retention ends. In 2026, retention policy is no longer a back-office records activity—it's a board-level risk topic that intersects with cybersecurity, privacy, finance, and operational resilience.
The reality for many enterprises is fragmented content sprawl: contracts in email, invoices in shared drives, SOPs in departmental tools, HR files in legacy systems, and customer documents spread across cloud apps. When auditors or legal teams ask for proof, teams scramble. The cost isn’t just penalties—it’s lost productivity, delayed decisions, reputational damage, and increased exposure during litigation or breach investigations.
An ECM (Enterprise Content Management) retention policy in 2026 must do more than define time periods. It must enforce lifecycle rules across repositories, automate classification, support legal holds, protect record integrity, and make retrieval fast and explainable—especially as AI search and AI assistants become common access layers to enterprise content.
Why this matters today
Decision-makers are facing three simultaneous pressures:
1) Regulations are tightening and audits are accelerating
Retention requirements are expanding across financial records, privacy laws, industry standards, and cross-border obligations. Auditors expect evidence: retention schedules, access logs, immutable storage controls, and disposal proof.
2) Data volumes are growing faster than budgets
Uncontrolled storage increases cost, risk, and search complexity. “Keep everything forever” is expensive and often non-compliant, especially under privacy and minimization requirements.
3) AI changes how content is discovered and used
As teams adopt AI search and assistants, retention and permissions must be consistent and enforceable. Otherwise, AI may surface sensitive or expired records, creating a new class of compliance incidents.
A modern retention policy is ultimately a business continuity tool: it ensures evidence is available when needed, reduces risk exposure, and prevents operational bottlenecks caused by document chaos.
Key challenges in card blocks
Fragmented repositories
Policies exist on paper, but files live across email, shared drives, local devices, and cloud apps—making enforcement inconsistent and audits painful.
Manual classification and metadata gaps
Without accurate document type, owner, and retention category, automation breaks. Manual tagging becomes a bottleneck and a source of errors.
Conflicting requirements
Finance wants long retention; privacy wants minimization; legal wants holds. A single “retain everything” approach creates regulatory contradictions.
Weak disposition controls
If deletion is ad hoc and undocumented, organizations can’t prove defensible disposal, and risk retaining liabilities longer than necessary.
Audit trail limitations
Auditors increasingly ask for end-to-end evidence: who accessed what, what changed, what was retained, and why. Incomplete logs weaken trust.
Security and insider risk
Sensitive records often remain exposed beyond their need. Without least-privilege controls and monitoring, retention becomes a security liability.
Risks of weak retention (and why leaders should care)
For CTOs, Ops Heads, Compliance Heads, and Finance leaders, retention policy is about measurable risk reduction and predictable operations—not just compliance checklists.
Common enterprise-level consequences
- Regulatory penalties and audit findings: Lack of enforceable retention schedules and evidentiary logs can trigger fines, corrective actions, and increased audit frequency.
- Litigation and eDiscovery cost explosion: Over-retention increases the volume of discoverable material; under-retention creates spoliation risk and adverse inference.
- Privacy and breach exposure: Retaining personal or sensitive data beyond necessity raises breach impact and remediation costs.
- Operational slowdowns: Teams waste hours searching, validating versions, and re-creating lost files—delaying finance close, vendor onboarding, and contract cycles.
- Loss of trust: Customers and partners increasingly request evidence of information governance; weak retention undermines due diligence outcomes.
Deep-dive: What “ECM retention policy in 2026” really means
In 2026, retention is best understood as a content lifecycle system that continuously governs records from creation to disposition. A modern ECM retention program typically includes the following pillars:
1) Lifecycle states with enforceable controls
Documents move through states such as Draft → Approved → Record → Archived → Disposed. Each state has specific access, edit, versioning, and retention rules. For regulated items, once declared a record, content should be protected against unauthorized edits and tracked with immutable logs.
2) Retention schedules mapped to business and regulatory needs
A retention schedule is not a generic spreadsheet. It’s a living mapping between document categories (e.g., AP invoices, tax filings, quality records, HR personnel files, SOPs) and the required retention duration, triggers (creation date, closure date, termination date), and disposal actions.
3) Legal hold and exception management
When litigation, investigation, or audit occurs, retention policies must pause disposition for relevant content without disrupting the rest of operations. Legal holds should be targeted, auditable, and reversible.
4) Defensible disposition with proof
Disposal is not just deleting a file. It’s executing an approved, policy-driven disposition workflow, capturing authorization, timestamps, scope, and rationale—so you can prove the organization did not destroy evidence improperly.
Practical scenario: A finance team needs vendor invoices for statutory retention, while procurement wants supplier contracts searchable for renewals and risk clauses. A modern ECM links each document type to its retention, automates classification, and provides role-based access—so finance remains audit-ready and procurement remains operationally efficient.
Decision insight: Retention should be treated as a cross-functional operating model—owned by Compliance, enabled by IT, executed by business teams, and verified through reporting. If it’s “IT’s job,” it becomes a tool problem; if it’s “Compliance’s job,” it becomes a policy-only problem. In 2026, it must be both.
Solution approach: How to design an enforceable retention policy
An effective ECM retention program is built through structured decisions—not guesswork. The following approach is widely used in large enterprises to make retention measurable and enforceable:
- Inventory content and systems: identify repositories, business processes, document types, and owners (Finance, HR, Legal, Ops, Quality).
- Define retention categories and triggers: creation date vs. closure date vs. termination date; include event-driven triggers like project completion or policy supersession.
- Map regulatory and contractual obligations: consolidate requirements and resolve conflicts using documented precedence rules and exceptions.
- Design record declaration and access controls: decide when a document becomes a record and who can modify, approve, or release it.
- Implement legal hold workflows: target content via metadata, custodian, matter ID, or search criteria; preserve chain-of-custody evidence.
- Operationalize disposition: approvals, notifications, retention reports, and deletion certificates (or archive transfers) with audit trails.
- Measure and improve: dashboards for overdue reviews, orphaned documents, misclassifications, access anomalies, and hold effectiveness.
Feature breakdown (ECM-ready retention) using DIV cards
Centralized repository with controlled access
Store documents and records in a governed system with role-based permissions, minimizing shadow copies and uncontrolled downloads.
Retention schedules and policy rules engine
Configure retention periods, triggers, exceptions, and automatic actions—applied consistently across departments and document types.
Record declaration & version control
Ensure final/approved versions are preserved as records, with complete version history and controlled changes.
Legal hold and matter management
Pause disposition on specific content during litigation, audits, or investigations while keeping normal retention running elsewhere.
Immutable audit trails and reporting
Prove who accessed, edited, approved, exported, or deleted content—backed by comprehensive logs and compliance dashboards.
Workflow automation
Automate approvals, review cycles, retention reviews, and disposition tasks so policy isn’t dependent on human memory.
Secure search and retrieval
Find records quickly using metadata and content search while respecting permissions—critical for audits and operational response.
Disposition controls with proof
Enable defensible deletion/archival with approvals, retention certificates, and clear visibility into what was disposed and why.
Traditional vs modern retention (comparison using DIV cards)
Traditional approach (policy-only)
• Retention schedule in spreadsheets or PDFs
• Manual tagging, inconsistent naming
• Shared drives and email archives as “systems”
• Deletion happens ad hoc (or never)
• Audit responses are reactive and time-consuming
Modern ECM approach (policy + enforcement)
• Retention rules implemented in the ECM system
• Automated classification and validation workflows
• Role-based access, versioning, and record declaration
• Legal holds and defensible disposition built-in
• Faster audits with dashboards and immutable logs
Industry use cases (where retention policy becomes a competitive advantage)
Finance & Accounting
Retain invoices, tax filings, audit workpapers, and approvals with clear retention triggers (e.g., fiscal year close). Improve audit response times and reduce month-end close friction through consistent document retrieval.
Healthcare & Life Sciences
Control retention of patient records, lab reports, SOPs, validations, and quality documents. Support read-only record states and strict access boundaries for sensitive content.
Manufacturing & Quality
Maintain controlled documentation for inspections, certifications, equipment maintenance, deviations, and CAPA records. Reduce downtime caused by missing or outdated procedures.
Banking, Insurance & Financial Services
Ensure retention for KYC, onboarding documents, claims, policy records, and communications—while enforcing privacy and minimizing unauthorized access.
Public Sector & Education
Retain procurement records, citizen/student files, grants, and governance documents with clear disposition rules and transparency-oriented audit trails.
Implementation perspective (what leaders should plan for)
Retention is as much change management as it is technology. A successful rollout typically follows phased delivery so you start reducing risk quickly without disrupting operations.
Phase 1: Governance & design
Define retention owners, categories, triggers, approval paths, and legal hold process. Align Compliance, Legal, IT, and business units on decision rights.
Phase 2: Configuration & pilot
Implement retention rules for a high-impact area (e.g., Finance AP/AR, Contracts, or HR). Validate classification accuracy, search speed, and audit trails.
Phase 3: Scale & integrate
Expand to additional departments. Connect with identity providers, workflow tools, scanners, and line-of-business applications to reduce manual steps.
Phase 4: Optimize & automate
Introduce continuous monitoring, retention review cycles, exception reporting, and AI-assisted classification/search—while maintaining governance controls.
Leadership checkpoint: Ask for evidence of enforceability. A retention program isn’t “done” when the schedule is written—it’s done when the system can demonstrate that retention and disposition are happening consistently, with audit-ready reporting.
Business impact / ROI (how retention pays for itself)
Retention improvements deliver ROI in both cost reduction and risk avoidance. While the exact numbers vary, the value usually appears in five areas:
- Lower storage and admin overhead: Defensible disposition reduces unnecessary retention of redundant and obsolete files.
- Faster audits and reduced disruption: Searchable records and dashboards reduce audit preparation cycles and stakeholder distraction.
- Faster business cycles: Contract retrieval and version certainty speeds renewals, negotiations, and procurement decisions.
- Reduced legal exposure: Better holds and disposal reduce litigation costs and improve defensibility in disputes.
- Stronger security posture: Limiting access and retention reduces the “blast radius” of breaches and insider incidents.
Finance leader lens: Treat retention as a controls modernization initiative. The return is not only fewer penalties—it’s a measurable reduction in process time, audit man-hours, and risk-adjusted cost of incidents.
Future readiness: AI search, automation, and retention in 2026+
AI is reshaping enterprise search and knowledge work. But AI also amplifies governance gaps: if a document is misclassified, expired, or accessible to the wrong audience, AI can surface it instantly—at scale.
A future-ready retention policy should therefore include:
AI-assisted classification with human oversight
Use automation to propose metadata and categories, but keep approval controls for high-risk document classes and regulated records.
Permission-aware AI search
AI search should respect role-based access and retention states, ensuring users only see authorized, valid records.
Explainability and auditability
Leaders should require evidence of how documents were categorized, why retention rules were applied, and what actions were taken.
Policy-as-code mindset
Retention rules should be consistent, testable, and reportable—reducing ambiguity when organizations scale or expand globally.
In short: AI makes governance more valuable, not less. If your ECM retention foundation is strong, AI becomes a productivity multiplier. If your foundation is weak, AI becomes a compliance accelerator—in the wrong direction.
FAQs
1) What’s the difference between a document retention policy and an ECM retention policy?
A retention policy describes what should happen. An ECM retention policy operationalizes it through system rules, workflows, access controls, legal holds, and audit trails—so it actually happens consistently.
2) Should we keep everything to be safe?
Not usually. Over-retention increases legal discovery scope, storage costs, and privacy exposure. The safer approach is policy-driven retention with defensible disposal and strong legal hold processes.
3) How do we handle conflicting requirements (privacy vs finance vs legal)?
Use documented precedence rules and exceptions. For example, privacy minimization applies unless statutory finance retention requires longer storage; legal holds override disposition temporarily. The ECM should enforce these exceptions transparently.
4) What evidence do auditors typically expect?
Retention schedules, access/changes logs, proof of record integrity, retention application reports, legal hold history, and defensible disposition records (who approved, what was disposed, and when).
5) How long does it take to implement retention in an ECM?
Timelines depend on scope and readiness. Many organizations start with a pilot department in weeks, then scale across functions in phases—prioritizing high-risk/high-volume content first.
ECM retention policy 2026, enterprise content management retention, records management compliance, document management retention schedule, workflow automation for retention, legal hold, audit trail, secure AI search, governance risk and compliance, defensible disposition, document lifecycle management, data minimization, privacy compliance, secure document repository, version control, role-based access control.
Ready to modernize retention and become audit-ready in 2026?
If your teams are still relying on shared drives, manual tagging, and spreadsheet retention schedules, it’s time to move from “policy intent” to “policy enforcement.” A modern ECM-backed approach strengthens compliance, reduces risk, and improves operational speed—without adding complexity for end users.