Strengthen document security, access control, and audit readiness with modern enterprise content management.
enterprise document management, document security, secure document storage, secure document sharing, compliance document management, workflow automation, AI-enabled content operations, role-based access control, audit logs, encryption at rest, encryption in transit, document retention, records management, version control, approvals, SOP governance, ISO-aligned documentation, audit readiness, sensitive data protection, data loss prevention, controlled access, vendor document exchange, contract lifecycle security
Enhance Document Security with Robust Protection for Sensitive Data
Security failures rarely begin with “hackers.” They begin with everyday work: the wrong person gets the wrong file, a stale template is reused, an approval is skipped, or a confidential contract is emailed outside the company. When documents carry customer PII, supplier pricing, financial results, IP, clinical records, or employee data, those small cracks become expensive incidents.
Most organizations don’t lack effort—they lack structure. Files live across email, shared drives, chats, and personal desktops. Permissions are inconsistent. There’s no single, reliable audit trail. And when a customer, auditor, or regulator asks, “Who accessed this document, who approved it, and which version was sent?” teams scramble.
This guide explains what “robust document security” looks like in practice, why it matters now (especially in the AI search era), the workflow-level risks of doing nothing, and how a ShareDocs-style structured document management approach helps protect sensitive data without slowing your business down.
Why document security matters today
AI search changes the risk model
Enterprise search and AI assistants make it easier to find information fast—if permissions, metadata, and classification are correct. If they’re not, AI can inadvertently surface sensitive content to the wrong audience.
Compliance expectations keep rising
Auditors want evidence: access logs, retention rules, version history, and approval traceability. “We think only Finance has access” is not acceptable proof.
Scale makes informal processes break
What worked for 50 people fails at 500. More documents, more vendors, more remote work, and more handoffs increase exposure unless controls are standardized.
Buyers expect strong controls
Customers increasingly ask how you manage data: secure sharing, access governance, retention, and auditability. Document security becomes part of winning deals.
What is document security?
Document security is the set of policies, controls, and technologies that ensure only authorized people can access, edit, share, and retain documents—while providing traceable evidence of what happened to each file across its lifecycle.
Key challenges enterprises face (and why they persist)
1) Permission sprawl
Shared drive folders, ad-hoc links, and copied files create “ghost access.” When employees change roles or vendors rotate, old permissions often remain.
Buyer impact: increased risk of accidental exposure and slower audits.
2) No consistent classification
Teams store contracts, invoices, HR records, and engineering drawings together without labels like “Confidential,” “Restricted,” or “Public,” making automation and enforcement difficult.
Buyer impact: controls are manual and unreliable.
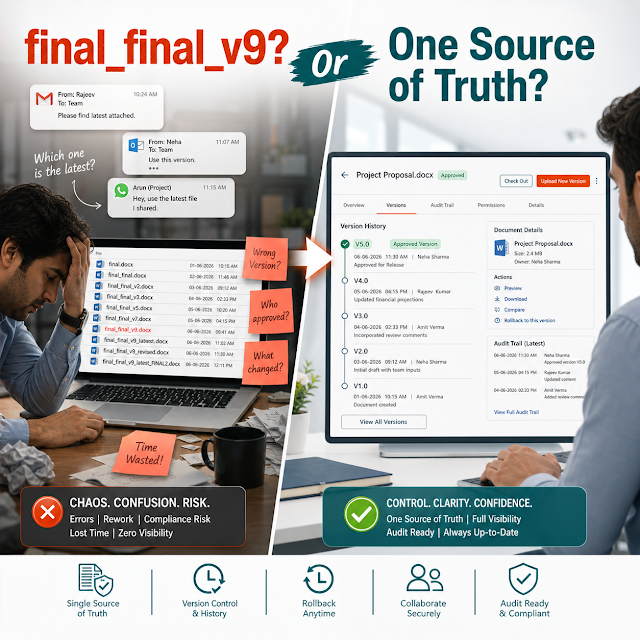
3) Version confusion
“Final_v7_reallyfinal.pdf” is not governance. Without versioning and check-in/out controls, teams reuse outdated templates, policies, and price sheets.
Buyer impact: mistakes in customer deliverables and approvals.
4) Weak audit readiness
If access logs, approvals, and document history are spread across tools, it’s hard to prove who did what. Audits become fire drills.
Buyer impact: higher compliance cost and operational distraction.
5) Uncontrolled external sharing
Email attachments and open links lack expiry, tracking, and consistent restrictions. Sensitive data leaves your environment without guardrails.
Buyer impact: exposure risk with vendors, partners, and customers.
6) Retention and deletion gaps
Keeping everything forever can be as risky as deleting too soon. Without retention policies, organizations fail to meet legal requirements or increase discovery risk.
Buyer impact: legal exposure and higher storage + search noise.
The risks of doing nothing
- Data breach and notification costs: one exposed folder can trigger incident response, legal review, and reputational damage.
- Non-compliance penalties: regulators and customers may require provable controls, not verbal assurances.
- Revenue risk: security questionnaires and procurement reviews can stall or block deals if document governance is weak.
- Operational drag: teams waste time searching, confirming latest versions, and redoing approvals.
- Litigation and discovery risk: uncontrolled retention increases what you must produce and review during disputes.
Deep-dive: how security gaps disrupt real workflows
Document security isn’t only an IT concern—it shows up inside day-to-day execution. The most common failures occur where work changes hands: intake, review, approval, sharing, and retention. Below are practical examples of how small control gaps become major problems.
Procurement and vendor onboarding
Vendor contracts, tax forms, insurance certificates, and compliance attestations often arrive via email. If files are saved into generic folders, it becomes unclear which vendor version is current, who approved the terms, and whether confidential pricing is restricted.
Result: delays in onboarding, repeated follow-ups, and accidental disclosure of pricing or bank details.
Finance close and audit prep
Month-end close generates statements, reconciliations, and supporting evidence. If approvals are done in chat and files are emailed, auditors struggle to trace the evidence chain—especially when older files are overwritten.
Result: longer close cycles and high audit fees due to manual sampling and rework.
HR and employee lifecycle
Offer letters, ID proofs, background checks, and compensation files must be protected with strict access. If HR stores documents in broad-access folders, “internal curiosity” becomes a compliance and trust issue.
Result: privacy incidents, policy violations, and reputational damage with employees.
Quality management and SOP updates
SOPs and controlled documents require version control, approvals, training acknowledgements, and effective dates. When teams circulate PDFs manually, old versions keep resurfacing in operations.
Result: process deviations, non-conformances, and failed audits.
Why it matters (workflow perspective)
When security is bolted on after the fact, it slows work and gets bypassed. When security is built into structured document workflows—classification, permissions, approvals, and audit trails—teams move faster because the “right way” is also the easiest way.
A practical solution approach: structured document management
Robust protection for sensitive data typically requires more than one control. The most successful enterprises combine policy (what should happen), process (how it happens), and platform controls (what the system enforces).
A ShareDocs-style approach focuses on securing the document lifecycle end-to-end:
capture → classify → store → collaborate → approve → share → retain → audit.
Each step reduces risk while improving speed and accountability.
How it helps
Structured document management helps by enforcing least-privilege access, maintaining a single source of truth with version control, enabling secure internal and external collaboration, and producing audit-ready evidence without manual effort.
Feature breakdown: what “robust protection” should include
Role-based access control (RBAC)
Restrict view/edit/download rights by department, role, project, and document type. RBAC prevents “everyone in the folder can see everything.”
Buyer value: reduces accidental exposure while simplifying user provisioning.
Secure sharing with control
Share documents externally with restricted links, expirations, and clear permissions. Reduce email attachments and avoid uncontrolled copies.
Buyer value: supports vendor/customer collaboration without losing governance.
Audit trails and activity logs
Track who accessed, edited, approved, shared, or deleted documents. Audit trails turn “we believe” into evidence.
Buyer value: faster audits, quicker investigations, and improved accountability.
Version control and single source of truth
Maintain a reliable version history with check-in/check-out or controlled editing. Prevent outdated templates from re-entering workflows.
Buyer value: fewer errors in customer-facing and regulated documentation.
Workflow automation for review & approval
Route documents to the right approvers with due dates, reminders, and escalation. Capture approval decisions and timestamps automatically.
Buyer value: faster cycle times and provable governance.
Retention rules and controlled disposal
Keep documents for the required period by type (contracts, HR, finance) and apply defensible deletion where appropriate.
Buyer value: reduces legal risk and keeps search results clean and relevant.
Comparison: unmanaged storage vs structured document security
Unmanaged file storage (typical state)
Access: folder-based, inconsistent, hard to review
Sharing: email attachments and long-lived links
Versions: duplicates and overwritten files
Approvals: chat/email approvals with poor traceability
Audit evidence: manual reconstruction across tools
Retention: “keep everything” or ad-hoc deletion
Structured document management (target state)
Access: RBAC + least privilege by document type
Sharing: controlled external access with governance
Versions: single source of truth with history
Approvals: automated workflows with timestamps
Audit evidence: system logs + searchable traceability
Retention: enforceable policies and defensible disposal
Industry use cases (realistic scenarios)
Manufacturing
A plant updates a work instruction (WI) and must ensure only the latest revision is used on the shop floor. A structured system locks old revisions, routes approvals to QA, and keeps an audit trail for certifications and customer audits.
Outcome: fewer non-conformances, faster audits, and reduced rework.
Healthcare & clinics
A multi-location clinic manages patient forms, insurance documents, and referral letters. Fine-grained access ensures only authorized staff can view restricted records, while logs provide evidence during incident reviews.
Outcome: stronger privacy posture and reduced exposure from misrouted documents.
Financial services
A lending team processes applications and supporting financial statements. Controlled sharing allows customers to upload documents securely, while retention policies ensure records are stored for required periods without indefinite exposure.
Outcome: faster processing with stronger compliance and auditability.
Construction & real estate
Projects involve drawings, permits, change orders, and vendor invoices. Version control prevents crews from using outdated drawings; controlled external access keeps subcontractors aligned without exposing internal cost data.
Outcome: fewer disputes and smoother handovers at closeout.
IT & software teams
Security policies, architecture diagrams, and incident reports should be restricted to specific roles. A structured system prevents wide distribution and keeps an evidence trail for certifications and customer security reviews.
Outcome: quicker responses to security questionnaires and renewals.
Education & administration
Administrative offices handle staff records, student data, and contracts. Segmented access and audit logs reduce the risk of internal exposure while improving retrieval speed for authorized users.
Outcome: safer operations and less time lost searching across systems.
Implementation perspective: how to roll out secure document management
Strong security programs succeed when they start with high-risk, high-volume document flows and expand. The goal is to improve controls while making work easier for teams.
Step 1: Map document types and risk
Identify sensitive categories (PII, contracts, finance, HR, IP) and where they live today. Define who should access what—and why.
Step 2: Define metadata and naming standards
Use consistent fields like document type, department, project, vendor/customer name, effective date, and confidentiality level for better control and search.
Step 3: Build role-based access templates
Create reusable permission sets by function (Finance, HR, Procurement) and apply them consistently. Automate access changes as roles change.
Step 4: Automate the highest-impact workflows
Start with review/approval flows that create the most friction: contracts, SOPs, vendor onboarding, invoices, and policy updates.
Step 5: Set retention policies and audit routines
Define retention by document class and implement periodic access reviews. Treat audit trails as a daily operating tool, not an annual scramble.
Step 6: Train users with “secure by default” habits
Show teams how to store, share, and approve documents in the system. Remove unofficial routes (email attachments) by making the secure path faster.
Business impact and ROI: what you can measure
A secure enterprise document management program should deliver measurable outcomes across risk reduction, speed, and customer confidence. Practical ROI often comes from fewer hours wasted and fewer costly mistakes.
Reduce time spent searching
Metadata, consistent structure, and a single source of truth reduce time spent hunting for the latest version or the right attachment.
Metric: average retrieval time per document type.
Speed up approvals and reduce rework
Automated routing and clear status reduce back-and-forth and ensure the correct stakeholders sign off before sharing externally.
Metric: approval cycle time; number of resubmissions.
Lower audit cost and disruption
When logs and histories are centralized, audits become evidence retrieval rather than investigation.
Metric: audit prep hours; external audit findings.
Reduce exposure from external sharing
Expiring links, controlled downloads, and tracking reduce the risk of sensitive files circulating without visibility.
Metric: number of external shares; expired vs active links; incidents.
Improve deal confidence
Strong security controls shorten security reviews and demonstrate maturity to customers and partners.
Metric: time to complete security questionnaires; win rate on governed deals.
Future-readiness: security in the age of AI-enabled content operations
AI can accelerate knowledge work—but only when your document foundation is governed. If your environment contains duplicates, unknown sensitivity levels, and inconsistent permissions, AI-powered search and summarization can amplify risk.
What is AI-enabled content operations?
AI-enabled content operations is the practice of using AI to find, summarize, classify, and route documents and knowledge faster—while maintaining governance through permissions, metadata, and auditable workflows.
How to prepare your documents for AI safely
Standardize metadata: document type, owner, sensitivity, and lifecycle stage.
Enforce permissions: AI should never override access rules; security must be inherited by search.
Reduce duplicates: a single source of truth minimizes conflicting answers and leakage.
Keep audit trails: track what was accessed and how outputs were derived.
The takeaway: security and structure are not obstacles to AI—they are prerequisites. The more your enterprise relies on AI search, the more you need compliance-grade document management.
FAQ: document security for sensitive data
1) What is the best way to protect sensitive documents in an enterprise?
The best approach is a structured document management system with role-based access control, versioning, secure sharing, audit trails, and retention policies—so security is enforced by default across the document lifecycle.
2) How do audit trails improve compliance document management?
Audit trails provide evidence of access, edits, approvals, and sharing. This reduces manual audit preparation and helps prove controls for regulated processes and customer security reviews.
3) Why is email a risk for secure document sharing?
Email attachments create uncontrolled copies, lack reliable expiration, and make it difficult to revoke access. Secure sharing replaces attachments with governed access and traceability.
4) How does workflow automation improve document security?
Workflow automation routes documents to the correct approvers, enforces required steps, and captures timestamps and decisions. This reduces bypasses and ensures sensitive documents aren’t shared before authorization.
5) How do I start improving document security without disrupting teams?
Start with one or two high-risk workflows (contracts, HR, finance, SOPs), implement standardized metadata and RBAC templates, and migrate active documents first. Make secure processes simpler than workarounds.
Ready to strengthen document security—without slowing work?
If you manage contracts, HR records, SOPs, finance evidence, or customer documentation, structured document management can reduce risk and improve speed at the same time. Explore how ShareDocs supports secure access, audit trails, and controlled workflows for sensitive data.
Learn more about ShareDocs:
https://sharedocsdms.com/