Data loss prevention in ECM helps protect documents, reduce leakage risk, and strengthen enterprise content security in 2026.
Data Loss Prevention in Enterprise Content Management: Protecting Documents in 2026
In 2026, “documents” are no longer passive files stored in a folder—they are living assets that move across email, chat, project tools, mobile devices, customer portals, AI assistants, and third-party collaboration channels. For most enterprises, the hard truth is this: the more productive the organization becomes, the more pathways exist for sensitive data to leak—accidentally or intentionally.
Data Loss Prevention (DLP) inside an Enterprise Content Management (ECM) platform is the control plane that keeps confidential information where it belongs. It helps ensure that regulated records, contracts, customer data, product designs, financial statements, HR documents, and legal artifacts remain protected—without turning the business into a slow, approval-heavy bureaucracy.
This article breaks down what modern DLP looks like in ECM, why it matters now, what risks leaders should care about, and how to implement a practical, measurable program that improves security and compliance while keeping operations fast.
Why this matters today
Enterprise leaders are under pressure from two sides: faster execution and stricter governance. Teams want frictionless sharing and instant access. Auditors, regulators, customers, and partners demand provable controls, traceability, and responsible data handling. Meanwhile, AI-enabled discovery and content generation are changing how people search, summarize, and reuse enterprise knowledge—often by pulling information from many documents at once.
DLP is no longer just “block USB copy” or “prevent email attachments.” In 2026, DLP must be embedded into the lifecycle of content: creation, classification, access, collaboration, retention, archival, and disposal. A modern ECM becomes the best place to implement DLP because it centralizes content, permissions, workflows, and audit logs—making governance enforceable and measurable.
For a CTO or CISO, the goal is to reduce breach probability and blast radius. For an Ops Head, the goal is to keep processes moving while reducing manual checks. For Compliance and Finance leaders, the goal is to prevent expensive incidents, ensure retention correctness, and prove defensible controls during audits, litigation, or investigations.
Key challenges (what breaks most DLP programs)
Content sprawl across tools
Sensitive documents are scattered across email attachments, local drives, chat apps, personal cloud storage, and shared folders—making consistent policy enforcement almost impossible.
Weak or inconsistent classification
If documents aren’t classified (confidential, restricted, public) and tagged with sensitivity, DLP rules become generic and either block too much or protect too little.
Over-permissioned access
“Everyone needs access” becomes the default. Excessive permissions are a major driver of insider risk and accidental exposure during collaboration.
Manual workflows and approvals
Paper-based or email-based approvals create blind spots. Security decisions are not logged, cannot be audited reliably, and cause delays that teams work around.
Limited visibility and auditability
Without centralized audit trails, leaders can’t answer: Who accessed what, when, from where, and what they did with it (view, download, share, delete)?
AI and search amplify exposure
AI search and summarization can inadvertently surface restricted information if permissions, redaction, and data boundaries aren’t enforced at the ECM layer.
Risks leaders should quantify (not just fear)
DLP is often framed as a security initiative, but decision-makers should view it as risk economics. When content is unmanaged, the organization pays repeatedly—through incidents, rework, audit findings, customer churn, and slowed execution.
Regulatory & compliance exposure
Non-compliance penalties, mandatory breach notifications, failed audits, and remediation programs that divert budgets for months.
Intellectual property leakage
Product specs, engineering drawings, pricing models, and strategic plans are high-value targets—often lost through routine sharing.
Insider threat & accidental exposure
Not every incident is malicious. Misaddressed emails, wrong folder uploads, public links, and excessive access are common causes.
Legal discovery and litigation risk
Inconsistent retention, missing audit trails, and uncontrolled copies increase eDiscovery cost and weaken defensibility in court.
A practical DLP program sets measurable outcomes: reduce unauthorized sharing events, reduce “unknown ownership” content, improve audit pass rates, shorten access approvals, and reduce time-to-investigate incidents.
Deep-dive: What “DLP in ECM” really means in 2026
Data Loss Prevention inside an ECM is the combination of policies, controls, automation, and evidence that prevents sensitive information from leaving authorized boundaries. These boundaries are not just network boundaries—they include user roles, business units, projects, customers, geographies, device types, and time windows.
A practical scenario
Your Finance team shares a quarterly forecast deck with leadership. A team member uploads the file into a general “Company Docs” folder for convenience. Without DLP, the deck could be accessible to a much wider audience than intended, copied externally, or indexed by enterprise search in a way that surfaces it to unauthorized users. With ECM-based DLP, the system can automatically classify the document as “Confidential – Finance,” restrict access to approved roles, watermark downloads, block external sharing, and log every view and download for audit readiness.
A mature DLP model also handles unstructured data (PDFs, scanned images, emails stored as files) using OCR and metadata extraction, so policy enforcement doesn’t depend on users “doing the right thing” every time.
Finally, DLP is not a single feature—it is a system of layered safeguards:
Prevent
Block risky actions: unauthorized download, public links, unapproved sharing, exporting, printing, or bulk extraction.
Detect
Identify sensitive content and suspicious behavior: mass downloads, unusual access times, access from new locations, or repeated permission changes.
Respond
Trigger workflows for approvals, incident handling, access reviews, and remediation with clear ownership and evidence.
Prove
Maintain audit trails, version histories, retention records, and reports that demonstrate policy enforcement.
Solution approach: Building DLP into your ECM program
Successful DLP programs don’t start with “turn on every restriction.” They start with business-critical content flows and the outcomes leadership needs: faster audits, lower incident rates, and secure collaboration. A proven approach:
Step 1: Identify high-risk document categories
Prioritize documents with financial impact, regulatory scope, or competitive value: contracts, invoices, employee records, compliance reports, customer data, supplier pricing, engineering documentation, and legal filings.
Step 2: Define a sensitivity model leaders can approve
Keep it practical: Public, Internal, Confidential, Restricted. Map each level to permitted actions (view/download/share/print), approval requirements, and retention rules.
Step 3: Automate classification and governance
Use metadata templates, OCR for scanned files, and policy rules that apply at upload/creation time. Reduce dependence on manual tagging.
Step 4: Enforce least-privilege access and secure sharing
Role-based access control (RBAC), group-based permissions, time-bound access, and approval workflows prevent “permission creep.”
Step 5: Build evidence for audits and investigations
Enable immutable audit logs, version history, watermarking, and retention schedules. Make reporting easy for Compliance and Internal Audit.
Feature breakdown: What to look for in an ECM with DLP controls
Centralized repository with governance
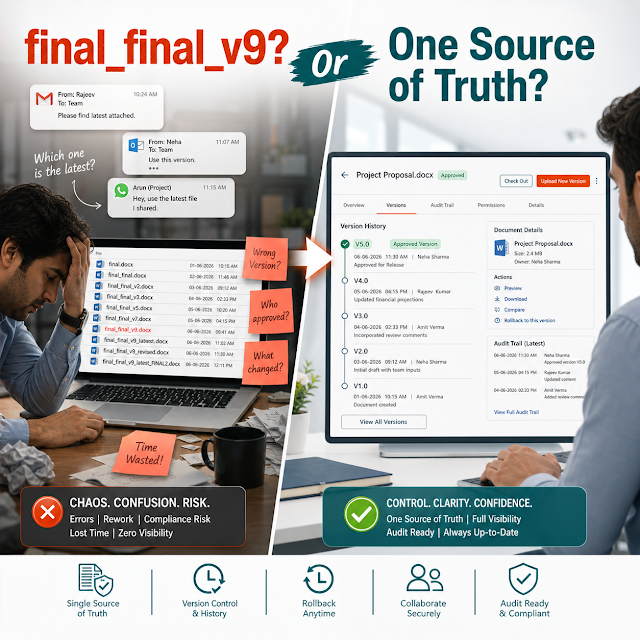
A single source of truth reduces uncontrolled copies. Folder structures, document types, and metadata make policy enforcement consistent.
Role-based access control (RBAC)
Restrict access based on roles, departments, projects, and need-to-know. Prefer groups over individual permissions for maintainability.
Granular permissions & secure actions
Separate view vs download vs print vs share permissions. Add controls like view-only access for highly sensitive records.
Workflow automation
Use approvals for external sharing, contract release, policy publishing, and finance closures—ensuring controls without slowing teams.
Audit trail, versioning, and traceability
Track who accessed, edited, shared, or deleted documents. Version history prevents “silent changes” and supports investigations.
Retention policies & legal hold readiness
Automate retention by document type and jurisdiction. Reduce over-retention (risk) and under-retention (non-compliance).
Encryption and secure storage
Protect data at rest and in transit. Ensure secure backups and controlled restoration processes.
Search with permissions (and safe AI search)
Search should never bypass access rules. AI summaries must respect document permissions and restrict sensitive excerpts.
Secure external collaboration
Share with vendors or customers using controlled access, expiry links, watermarking, and approvals—without sending attachments.
Traditional vs modern DLP: What changes in 2026
Traditional approach (common in legacy setups)
Perimeter-first controls
Focus on network boundaries, email filters, device restrictions.
Manual permissions
Access granted informally, hard to review and revoke systematically.
Limited audit proof
Logs are incomplete, spread across systems, difficult for auditors to trust.
Modern ECM-based approach (2026-ready)
Content-centric security
Controls follow the document lifecycle: classify, restrict, audit, retain.
Automated governance
Workflow automation, policy-based controls, consistent enforcement across departments.
Audit-ready evidence
Centralized logs, version history, retention schedules, and reporting for compliance.
Industry use cases (how DLP in ECM solves real operational problems)
Finance & shared services
Protect invoices, bank details, approvals, and audit artifacts. Enforce maker-checker workflows, retain records for required periods, and prevent unauthorized sharing of financial reports.
Impact: fewer reconciliation delays, stronger audit posture, reduced fraud risk.
Legal & contract management
Control access to contracts, NDAs, and negotiation documents. Keep version history and approvals, restrict downloads for sensitive negotiations, and support defensible legal holds.
Impact: lower litigation risk, faster contract cycles, reduced “lost clause” errors.
Healthcare & regulated records
Manage sensitive patient-adjacent documentation, insurance records, and compliance reports. Apply strict access and detailed audit trails for investigations.
Impact: improved compliance, reduced exposure during audits and incidents.
Manufacturing & engineering
Prevent leakage of designs, SOPs, supplier pricing, and quality documentation. Control external sharing with vendors through secure portals rather than email attachments.
Impact: reduced IP risk, improved supplier collaboration, better quality traceability.
HR & people operations
Secure employee records, payroll documents, performance reviews, and sensitive investigations. Enforce role-based access and retention rules automatically.
Impact: fewer privacy incidents, faster onboarding/offboarding, clearer accountability.
IT, security & compliance operations
Centralize policy documents, security evidence, vendor risk assessments, and audit responses. Use immutable logs and workflow trails for readiness.
Impact: shorter audit cycles, quicker investigations, reduced control failures.
Implementation perspective (what executives should demand)
Implementation success depends on aligning policy, technology, and operating model. A few executive-level principles:
Start with the highest-value workflows
Pick 2–3 processes where document leakage risk is real and measurable: contract approvals, invoice processing, compliance reporting, vendor onboarding.
Define ownership and escalation paths
If a document is flagged as restricted, who approves exceptions? Who investigates alerts? Without ownership, controls become noise.
Measure adoption and control outcomes
Track metrics like: percentage of classified documents, reduction in external attachment sharing, time to approve access, audit findings closed.
Plan integration and change management
ECM must fit daily work: capture documents from scanners, email ingestion rules, integrations with ERP/CRM where needed, and clear user training.
The leadership question is not “Can we secure everything?” It’s “Can we secure the most important information while making teams faster and more accountable?”
Business impact & ROI (how to justify investment)
The ROI case for DLP in ECM is typically strongest when framed around operational savings and risk reduction together:
1) Lower incident cost and investigation time
Central audit trails, versioning, and controlled sharing reduce the time security teams spend reconstructing events. Faster investigations mean lower business disruption.
2) Faster audits and fewer findings
Compliance teams spend less time hunting for evidence. Automated retention and immutable logs provide defensible proof of control enforcement.
3) Productivity gains through workflow automation
Maker-checker approvals, controlled external sharing, and standardized templates eliminate rework and reduce cycle time for finance, legal, and operations.
4) Reduced cost of uncontrolled storage and duplication
Centralizing content reduces duplicate copies across drives and mailboxes, lowers storage growth, and simplifies backup and retention management.
For Finance leaders, the strongest narrative is predictable: reduce audit effort, prevent avoidable incidents, and standardize document-driven processes to make outcomes consistent quarter after quarter.
Future readiness: DLP in the age of AI search and automation
AI is reshaping enterprise knowledge access. The risk is not only “a file is shared externally.” The new risk is sensitive information being surfaced indirectly through AI summaries, semantic search, cross-document answers, and automated recommendations.
A future-ready ECM must make AI safer by enforcing content permissions at every stage:
Permission-aware search and summaries
AI outputs must only reflect documents the user is allowed to access. This avoids “answer leaks” where restricted facts are revealed without opening the file.
Sensitive data boundaries
Restrict AI indexing for specific repositories (e.g., HR investigations, legal privilege, board materials) or require explicit approvals.
Better classification through automation
AI-assisted tagging can improve consistency, but must be governed with review workflows, auditability, and clear accountability.
In short: AI increases value from content—but it also increases the cost of weak governance. DLP inside ECM is how you enable AI safely, not how you stop innovation.
FAQs
1) Is DLP only a cybersecurity function?
No. DLP is a business governance capability. Security teams define and monitor controls, but Operations, Compliance, Legal, and Finance are key stakeholders because they own the processes and regulated records.
2) How do we prevent DLP from slowing teams down?
Use automation and risk-based controls: classify documents automatically where possible, apply role templates, and reserve approvals for external sharing or restricted content. The goal is consistent guardrails, not constant friction.
3) What’s the first workflow to secure for fast ROI?
Many organizations start with contract approvals, invoice processing, or compliance reporting because the document types are clear, the impact is measurable, and audit needs are immediate.
4) How does ECM-based DLP help with audits?
It creates reliable evidence: access logs, workflow approvals, document history, retention enforcement, and controlled sharing records—all in one system, reducing audit preparation time.
5) What should leaders ask vendors during evaluation?
Ask how the system enforces least privilege, handles external sharing, provides immutable audit logs, supports retention policies, prevents unauthorized downloads/prints, and ensures AI search does not expose restricted content.
Data loss prevention in enterprise content management, ECM DLP, secure document management system, workflow automation for compliance, audit trail and retention policy, AI search with permission controls, enterprise security and governance, secure document sharing, encryption, role-based access control, eDiscovery readiness, insider risk mitigation, information governance strategy 2026.
Ready to protect sensitive documents without slowing your business?
If you’re modernizing document management, strengthening compliance, or preparing for AI-enabled enterprise search, an ECM with embedded DLP controls is a practical next step. Centralize content, automate approvals, enforce least privilege, and keep audit evidence ready—so teams can move fast with confidence.